Replace the contact center with an autonomous agent fleet.
A national carrier handles ~200M billable customer interactions per year through an IVR, ACD, CRM, billing and dispatch stack. NxNxNxNxNx replaces every internal hand-off with an agent walk on the lattice — voice-in, action-out, in five hops or fewer.
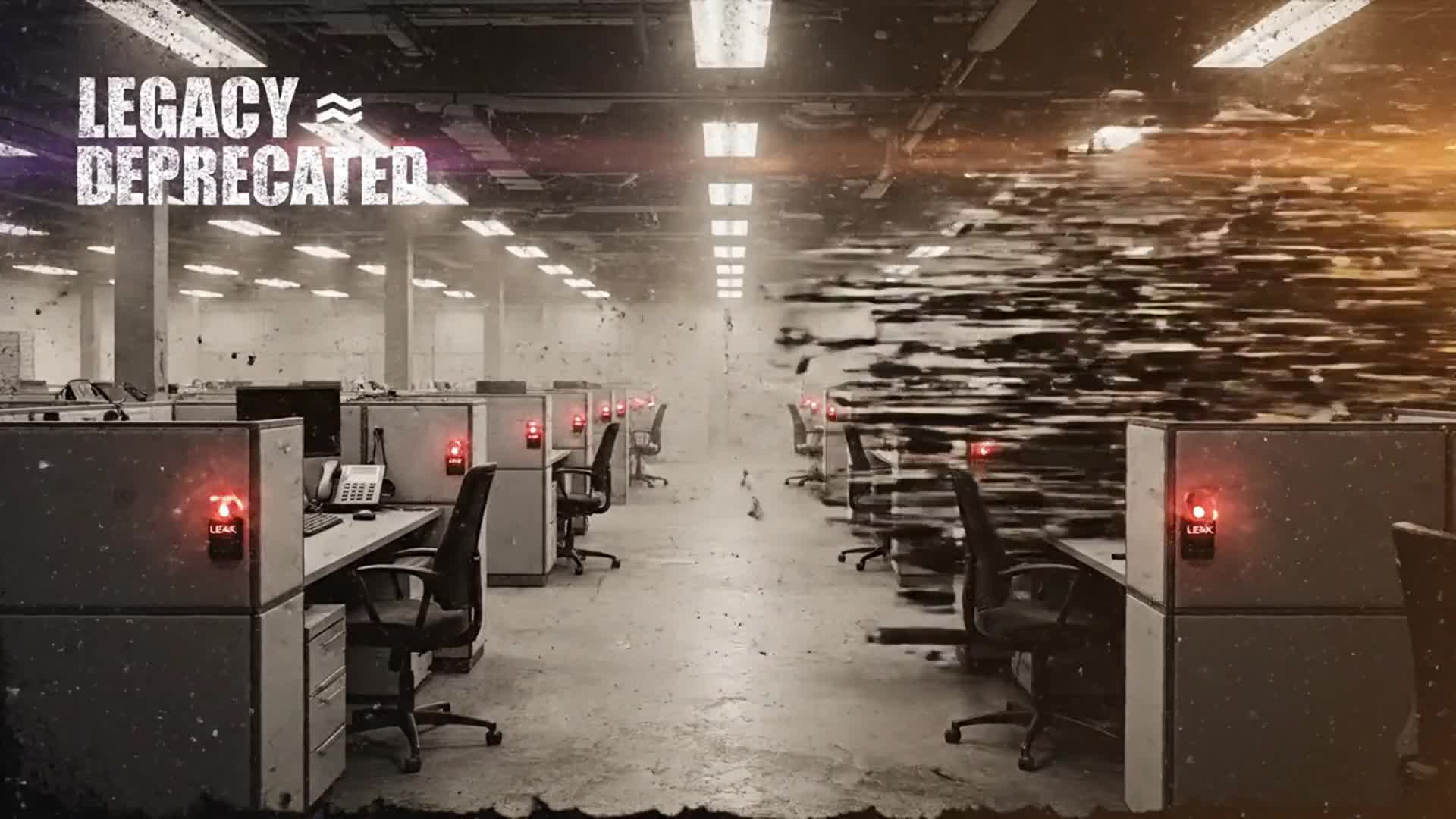
- Legacy IVR + ACD
- NxNxNxNxNx mesh